By Sjoerd van der Zwaan, chief product officer, Solid Sands
The brand new EU Regulation 2023/1230 is ready to enter drive on 20 January 2027, changing the long-standing Equipment Directive 2006/42/EC.
The implications for equipment producers are profound as a result of the regulation extends the scope of machine security to incorporate software-driven, autonomous, and AI-enabled techniques.
Consequently, the necessity to qualify machine software program and its toolchain as a part of a steady, lifecycle-based course of comes into sharp regulatory focus.
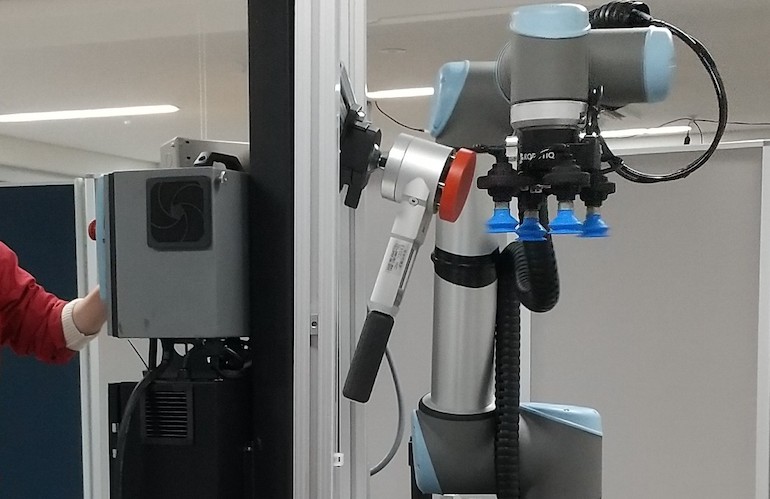
EU Regulation 2023/1230 extends obligatory security necessities to digital machine elements that had been beforehand addressed solely not directly. Embedded software program and AI performance for industrial robots and cobots (collaborative robots), and autonomous cell equipment now fall clearly inside the regulation’s scope.
For machine builders, it indicators a elementary shift. Software program is not an implicit contributor to security; it’s formally acknowledged as an express security element, with direct influence on qualification processes and ongoing compliance.
A brand new regulatory period When launching a machine into the industrial market, the producer is answerable for guaranteeing that its design and construct meet security necessities.
The corporate should undertake acceptable threat assessments and qualification actions, with high-risk equipment topic to third-party evaluate.
The regulation now makes clear that software-defined security parts require devoted compliance scrutiny, reinforcing the necessity to qualify not solely the appliance software program but in addition the software program toolchain used to create it.
Regulation 2023/1230 is carefully aligned with the EU’s AI Act and Cyber Resilience Act, forming a part of a broader shift towards a horizontal, lifecycle-based regulatory strategy targeted on sustained compliance.
Collectively, these frameworks place software program and its toolchain on the middle of machine security and compliance. Qualification is not a one-time certification milestone; it have to be demonstrated and maintained all through the operational lifetime of the machine.
From static compliance to steady assurance Traditionally, compliance adopted a predictable mannequin: producers certified their software program toolchain as soon as, froze it, licensed the product, and prevented modifications wherever doable. This strategy is more and more incompatible with trendy equipment.
Cybersecurity threats require ongoing patches and updates, and compilers and commonplace libraries change by means of bug fixes, efficiency enhancements, and language evolution. Locking these parts down indefinitely conflicts with regulatory expectations that emphasize sustained security assurance.
In parallel with the AI Act and Cyber Resilience Act, Regulation 2023/1230 displays this actuality. Software program is handled as a dynamic factor of the security case; cybersecurity is elevated to a security goal; and autonomous techniques interacting with human operators at the moment are topic to extra stringent conformity procedures.
Proof for steady assurance Below this new regulatory atmosphere, authorities anticipate proof that your complete software program improvement course of is managed, auditable, and reliable.
Compliance now depends upon demonstrating how security is maintained as techniques evolve. Slightly than freezing toolchains, producers should implement assurance practices that scale with change, supported by steady verification.
This shift elevates the significance of software program toolchain qualification. Compilers and libraries immediately affect useful correctness, determinism, and traceability in safety-related management techniques.
Optimization mechanisms, whereas important for efficiency and real-time constraints, might introduce refined dangers – for instance by altering numerical behaviour or execution paths in methods not seen at utility stage. Library defects also can propagate by means of points reminiscent of inconsistent information dealing with throughout codecs.
The excellence between assuming a software program instrument works and proving that it really works turns into essential. Below the regulation, software program is a traceable and assessable a part of the equipment security case, requiring demonstrable qualification.
Proof should prolong from system-level integration testing right down to the appliance software program, libraries, and compiler. Efficient assurance due to this fact depends on structured, repeatable testing of the toolchain in opposition to outlined specs.
Managing toolchain assurance
Toolchain qualification that delivers confidence throughout domains reminiscent of automotive and industrial is grounded in three real-life use circumstances: the continual qualification of compiler and commonplace library toolchains to keep up regulatory compliance over time; toolchain-centered high quality assurance, to scale back latent software program threat and anticipate as early as doable eventual later stage certification findings; and the continual integration (CI) of certified instrument chains.
CI environments implement using certified toolchains and seize the proof generated. Automated testing triggered by toolchain updates, configuration modifications, or scheduled regression cycles creates traceability between software program builds and qualification information.
This proof can assist the upkeep of an present security case and determine any deviations that require additional evaluation.
Closing the gaps
Regardless of the prolonged and well-publicized transition interval of EU Regulation 2023/1230, some equipment producers proceed to underestimate the dimensions of change required earlier than 20 January 2027.
Though their expertise with the Equipment Directive will present basis, the specific inclusion of software program, AI, and cybersecurity brings unfamiliar regulatory expectations.
Nevertheless, getting it proper will ship advantages that stretch far past authorized obligations. For example, steady toolchain qualification reduces latent threat, strengthens engineering confidence, and helps the secure deployment of autonomous and clever equipment.
It is because it exposes each strengths and limitations, permitting engineers to design techniques that keep away from identified weaknesses or deal with them proactively.
Figuring out toolchain points early gives choices: adapting code, participating with instrument suppliers, or deciding on various variations. It additionally avoids the invention of points late within the compliance course of, negating any potential forcostly redesign and recertification efforts.
In brief, steady toolchain qualification can grow to be a aggressive benefit fairly than only a regulatory tick-box train.
Time to behave
The brand new EU Regulation 2023/1230, along with the AI Act and Cyber Resilience Act, indicators the tip of the normal freeze-assess-qualify mannequin. Instead emerges a lifecycle-based strategy constructed on steady qualification, steady high quality assurance, and automatic proof technology.
For machine builders, adapting to this mannequin isn’t optionally available. It’s the authorized basis for putting secure, compliant, and future-ready equipment on the European market.
To start the transition, equipment producers ought to undertake a three-step technique. First, put the toolchain entrance and middle of tasks to keep away from hidden dangers, the potential for which solely will increase when deploying a posh ecosystem of AI and cybersecurity.
Machine builders want confidence of their toolchains to permit most deal with the event of utility software program and the combination testing thereof.
Second, begin migrating to this new technique as quickly as doable because it helps the early detection of issues and their simpler decision. It might even keep away from latent points that solely manifest after manufacturing commences. Undetected, these points can doubtlessly result in dangers of precise bodily hurt, pricey remembers, and harm to model fame.
Lastly, hold the lifecycle strategy in thoughts: steady high quality assurance and steady qualification – automated inside CI pipelines.
Stable Sands may help machine producers adjust to the EU Regulation 2023/1230 by means of the corporate’s confirmed take a look at, validation and qualification suites: SuperTest for C and C++ compilers; and SuperGuard for C and C++ libraries. Each suites can be found as a cheap, subscription-based fee mannequin.

In regards to the creator: Sjoerd van der Zwaan is a expertise chief specializing in synthetic intelligence, pc imaginative and prescient, and robotics, with in depth expertise constructing and scaling engineering groups and delivering customer-focused options. He’s chief product officer at Solid Sands, and his work focuses on shaping product methods that bridge superior technical capabilities with real-world buyer wants.